Remote Access VPN - Windows Client - ikev2
Scope: Access Remote Access VPN from Windows
Method: ikev2 (EAP)
For using EAP authentication, SSL certificates can be uploaded before selecting EAP authentication. The purpose of the certificate is to authorize the server. Both the certificates generated by the Certification Authority and the self-signed certificates can be used here.
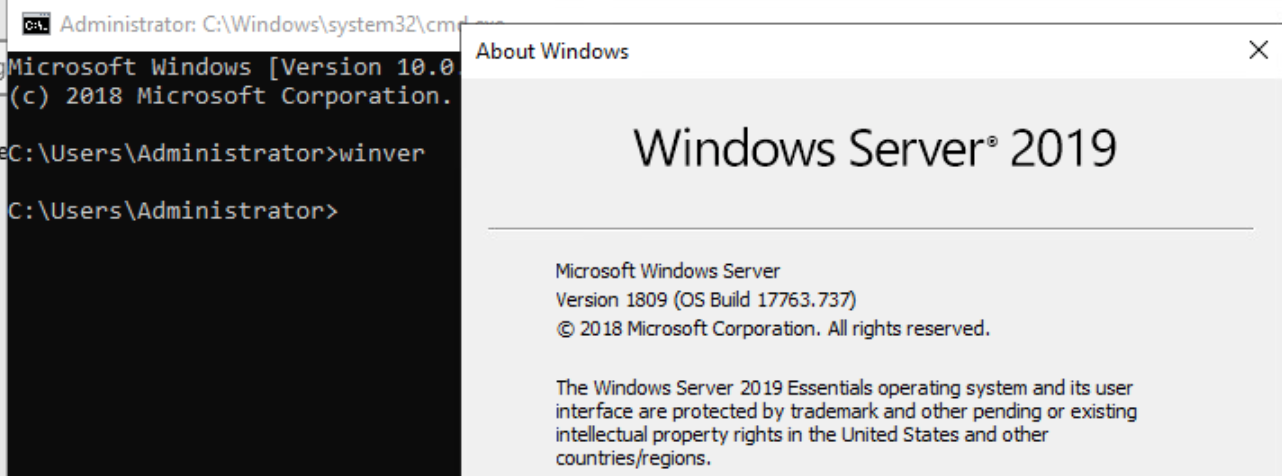
OS: Windows 2019
Expected: VPC is already configured and Source NAT is present
Steps:
-
Add SSL Certificate.
- Certificate
- Private Key
- If Password is configured for Private key then, use that in last while adding Certificate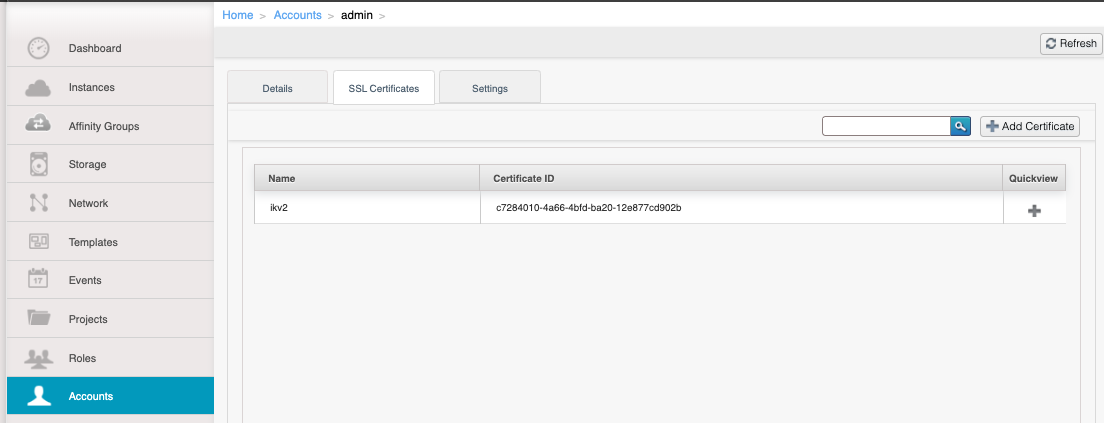
In order to generate self signed certificates the following instructions can be used.
- Create a open ssl certificate using the following command
openssl req -x509 -newkey rsa:2048 -keyout key.pem -out cert.pem -days 365
or if no encryption is required
openssl req -newkey rsa:2048 -new -nodes -x509 -days 3650 -keyout key.pem -out cert.pem - Upload the certificate to the account as mention above
-
Package the certificate along with key in p12 format to be used in windows client.
openssl pkcs12 -export -inkey key.pem -in cert.pem -out cert_key.p12
- Create a open ssl certificate using the following command
-
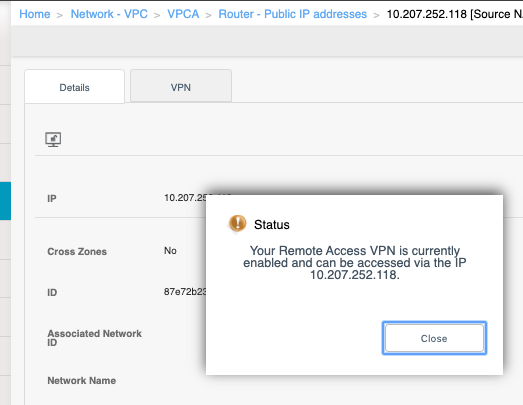
Enable Remote Access VPN as follow.
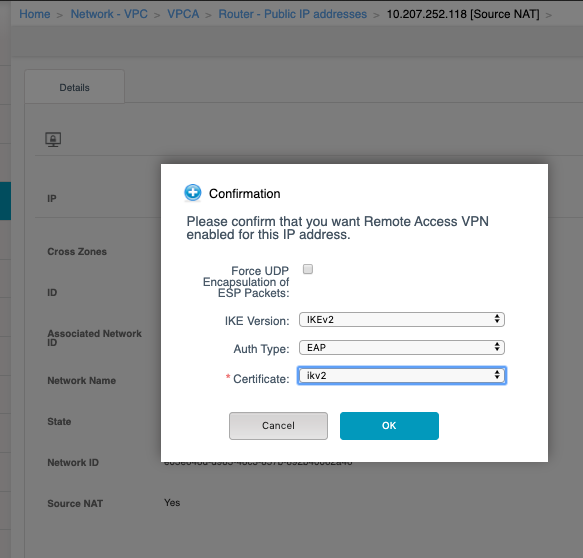
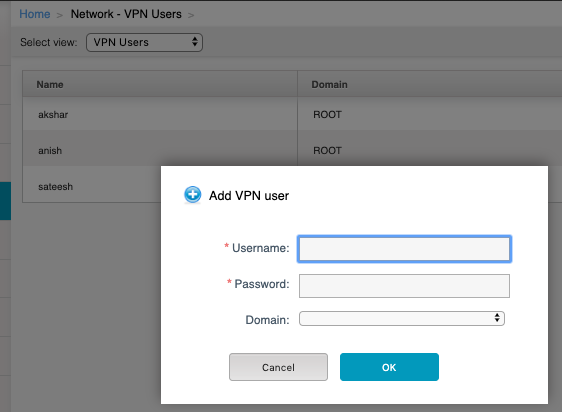
- Create VPN User If not available.
Windows Client Configuration
On the windows client , following steps needs to be performed
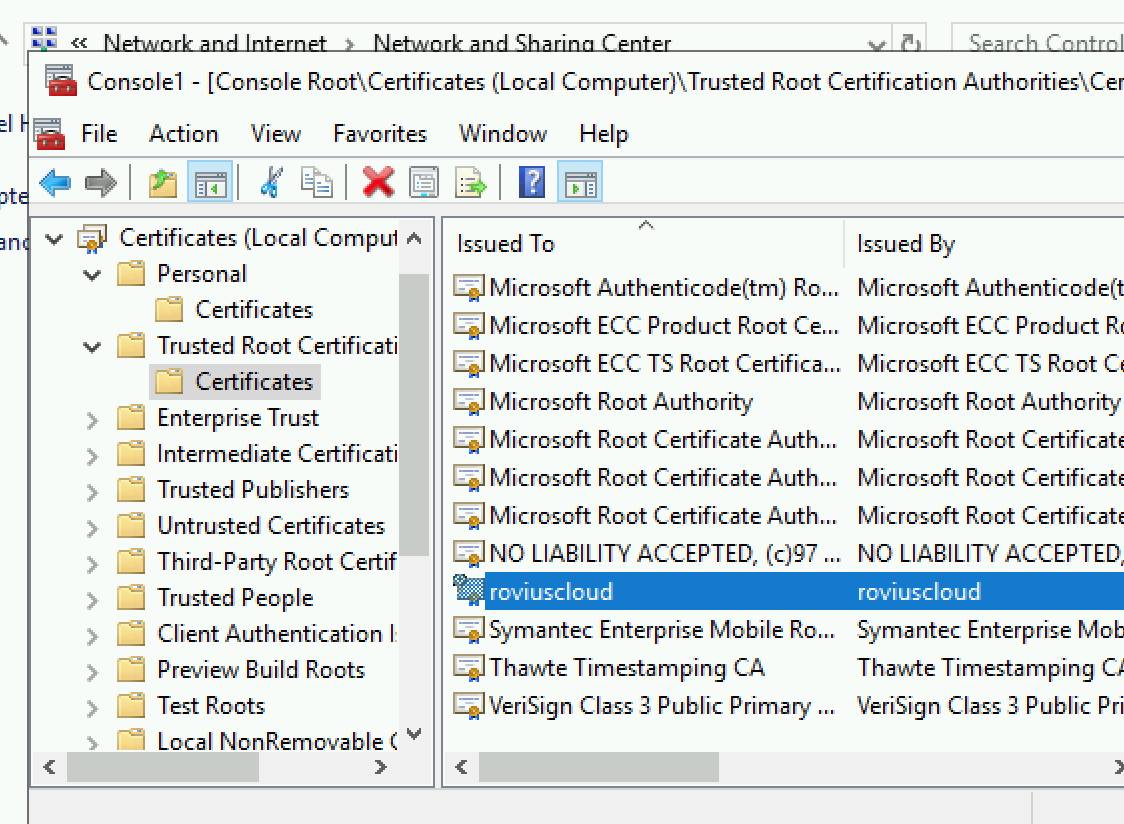
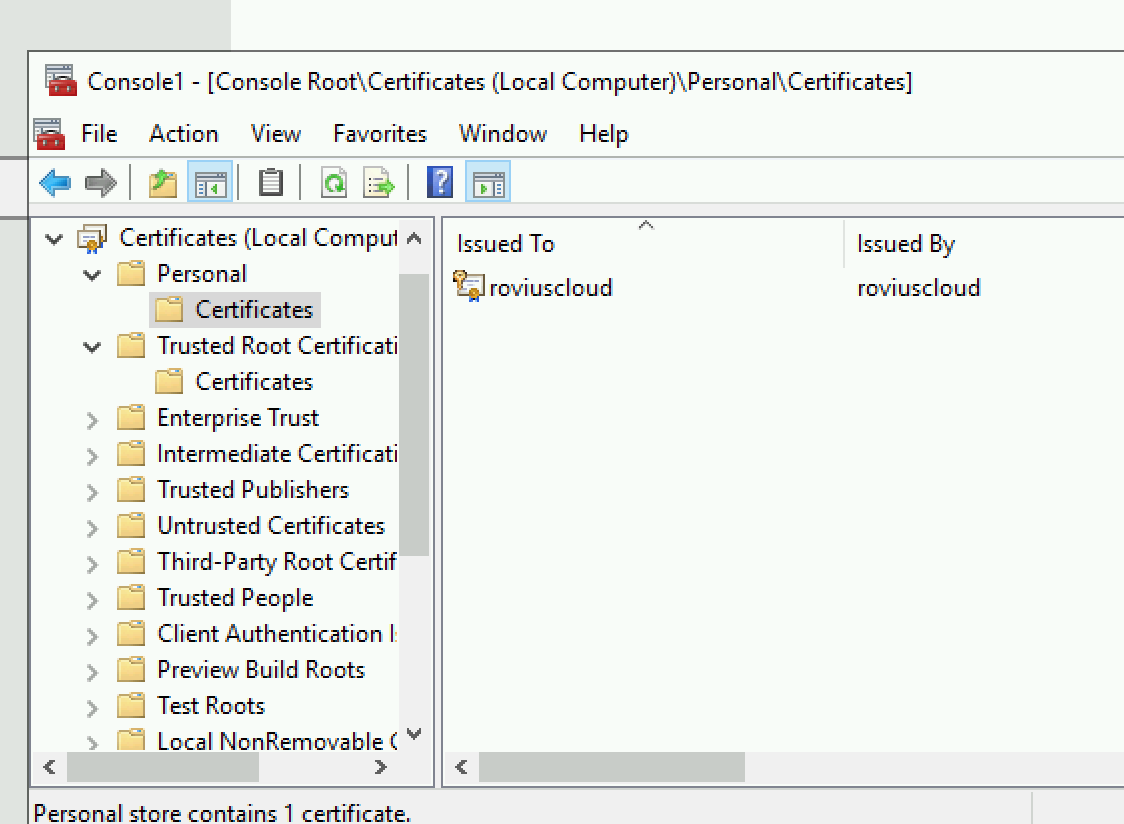
- Install the server certificate previously created (cert_key.p12) in the windows client
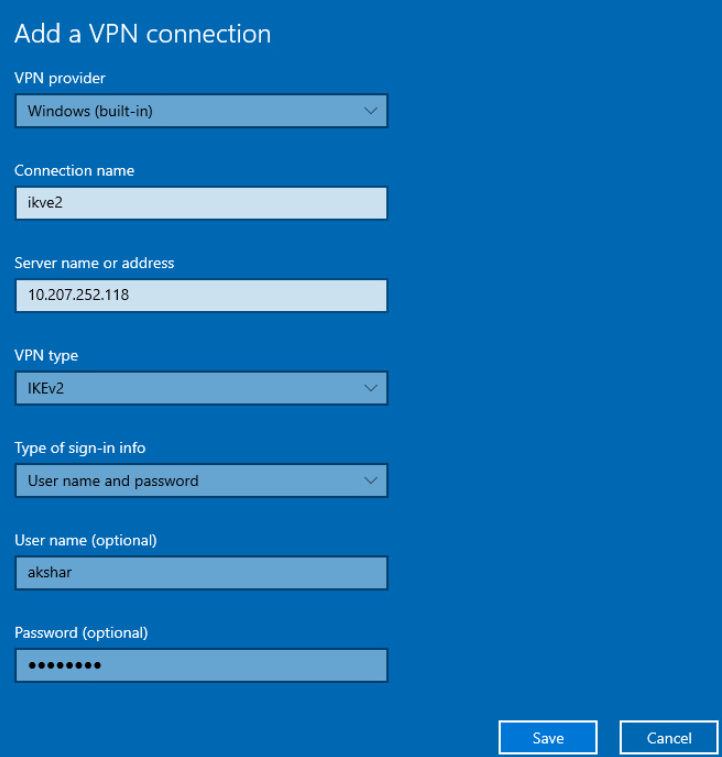
- Create a new VPN connection with VPN type as ‘ikev2’ to VPN gateway with Remote access VPN gateway IP address
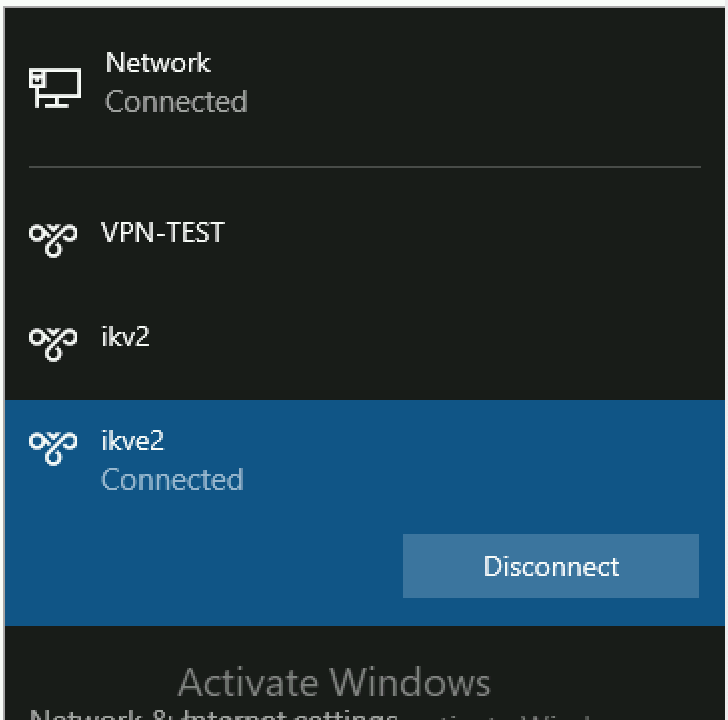
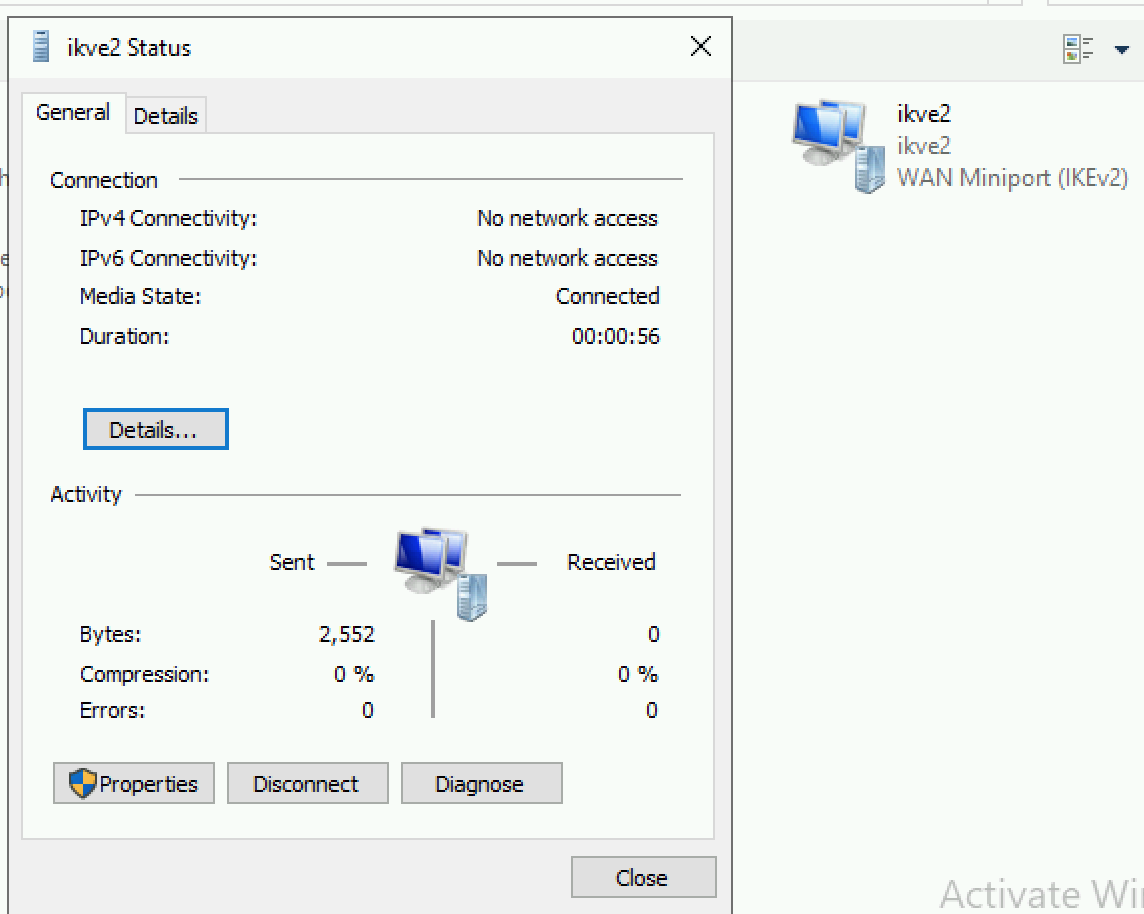
Status of VPN connection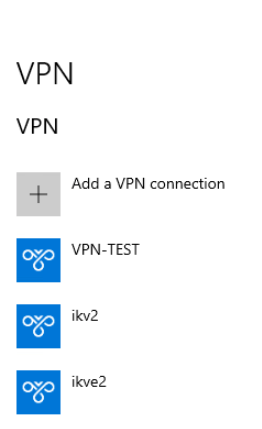
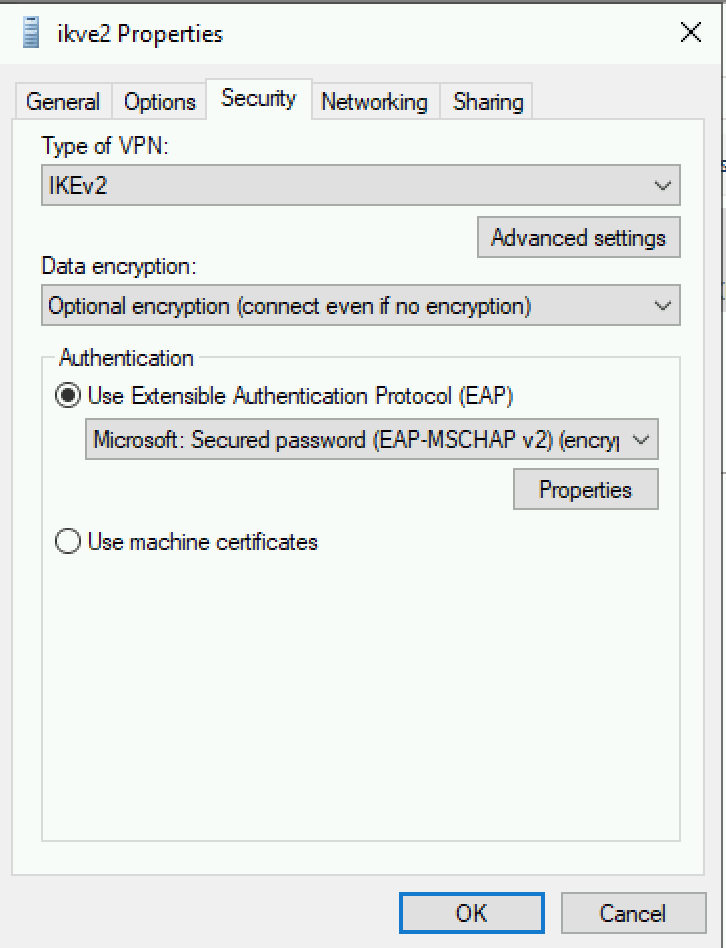
Right Click on the recently created connection and choose Properties.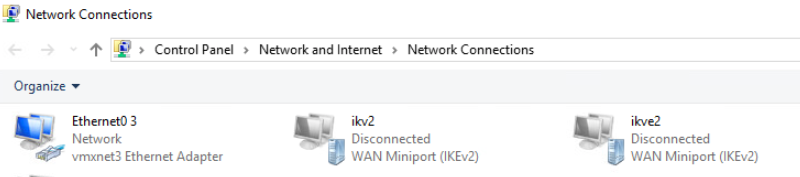
- Select EAP as the authentication method and EAP-MSCHAP v2 as the authentication method
- Go to the registry path HKLM/SYSTEM/CurrentControlSet/Services/RasMan/Parameters and Set DisableIKENameEkuCheck to 1
(Registry is attached in this doc. download that to a windows box and run command {Reg import FileName})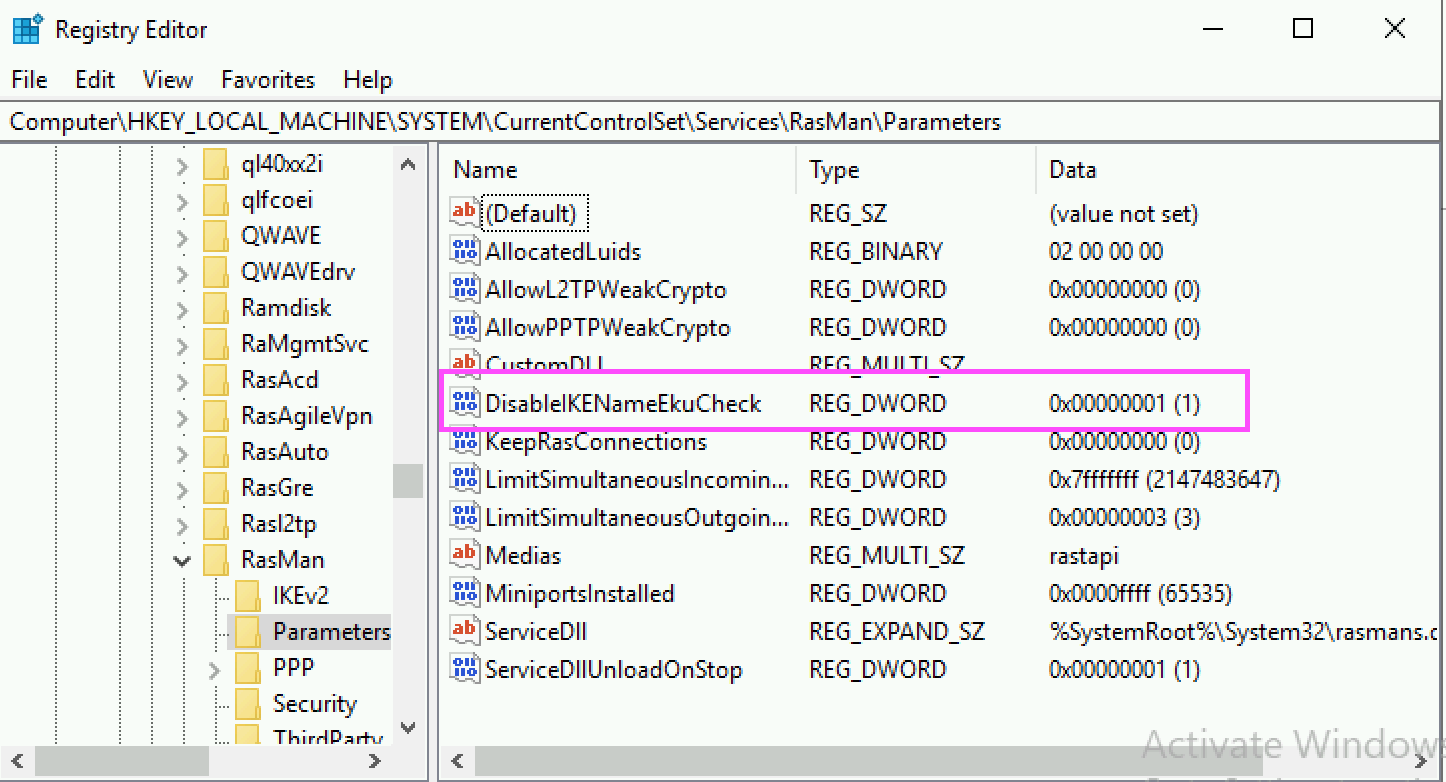
-
Try connecting and it would ask for the credentials. Provide credentials of one of the vpn users
-
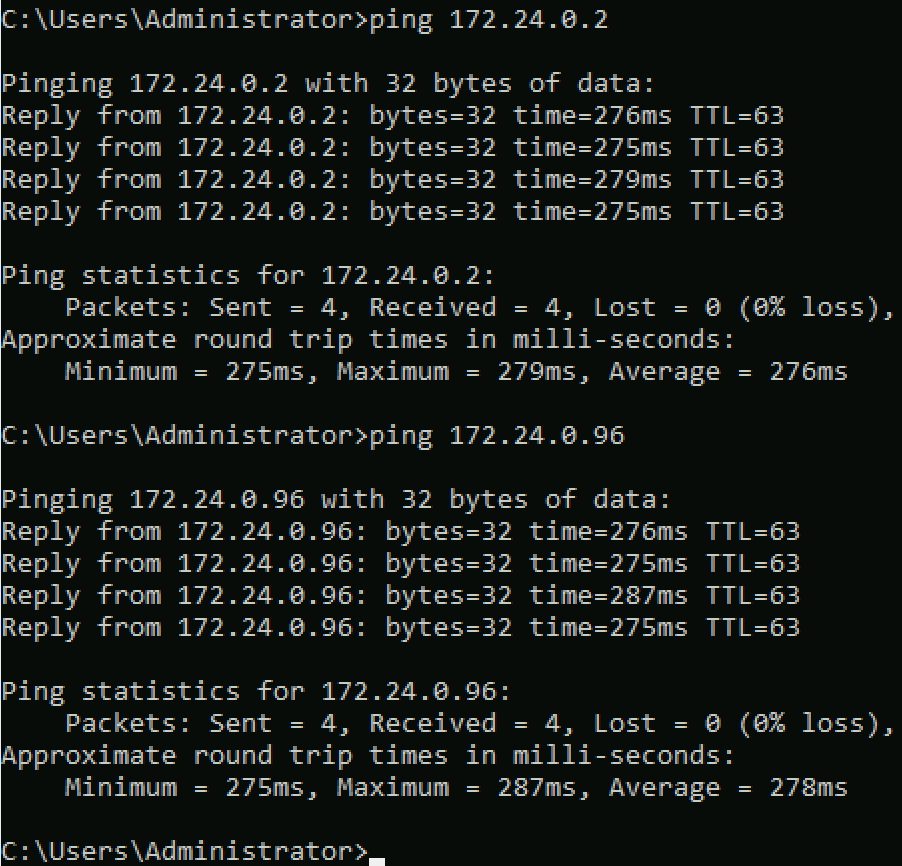
Check Route and Add route.
C:\Users\Administrator>route ADD 172.24.0.0 MASK 255.255.0.0 10.9.1.1
OK!
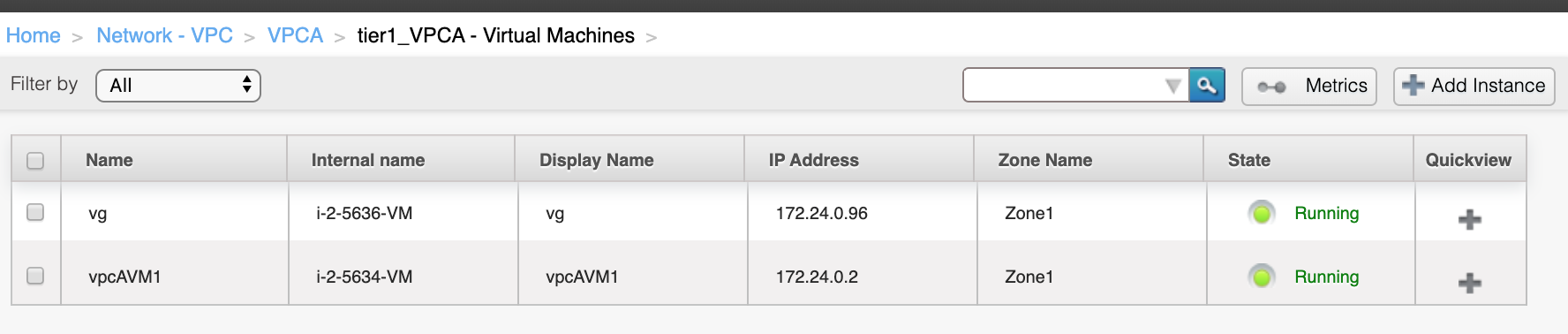
- Check VMs which are available in this VPC.
-
Router Side:
|
root@r-5475-VM:~# ipsec status |
|---|
|
root@r-5475-VM:~# ip xfrm state
|
|---|
Note: virtual IP range is configured using the parameter remote.access.vpn.ikev2.vip.cidr. The default value of the same is 10.9.1.0/24. In case, it is conflicting the private range, the same needs to be updated.
Registry Download:






Comments